Editor’s Note: This is an updated and expanded version of my original article on Granite State Taxpayers.
Electronic voting without paper ballots is a terrible idea. It destroys confidence in election integrity and invites malfeasance. It’s time to drive a stake through the heart of electronic voting once and for all.
TL;DR
- A genuinely secure election requires trust, anonymity, and accountability. Electronic voting destroys trust and accountability.
- Cybersecurity flaws don’t need to be exploited to undermine an election. They only need to exist, which is enough to create reasonable doubt of integrity.
- Blockchain does not fix this problem for many reasons.
- Paper ballots provide trust, anonymity, and accountability.
- Restoring trust will require an over-correction in the direction of transparency and accountability.

Why Electronic Voting is a TERRIBLE Idea
I’ve included two videos about election security by Tom Scott below for your information and viewing pleasure. The first video is one that I’ve been sharing with people FOR YEARS. I’ve been sounding the alarm bell against electronic voting for a long time. As the country becomes more polarized and elections become more disputed, the call for electronic voting seems to be increasing. I highly recommend watching the two videos below for more details about exactly why this would be a disaster.
Thankfully, in Iowa’s caucuses, only a handful of the 1,990 delegates required for one party’s nomination were at stake. We’ve been given a great gift; a vision of what elections could be like with widespread electronic voting.
Election Security Lessons from Iowa
Ohio State football coach Woody Hayes is credited with the adage that, “There are three things that can happen when you throw a pass, and two of them are bad.” When electronics are used for voting, there are four things that can happen, and three of them are catastrophic. All three election security nightmares happened in Iowa:
- Vote tabulating can be compromised
- Vote reporting can be compromised
- Confidence can be undermined
I won’t go into detail about all of the failures of the app, because they are well-documented. We know that it was poorly designed, people had trouble using it, it had massive security vulnerabilities, warning signs were ignored, and the numbers reported were riddled with errors and inconsistencies.
The vote tabulation itself was compromised. We’ve seen reports that many caucus chairs had trouble installing the app and logging in to it. The vote reporting was compromised because some caucus chairs could not get a wireless signal in order to connect to the central database. The New York Times reported discrepancies between numbers recorded in the app and actual caucus results.
But finally and (arguably) most importantly, trust in the process was blown to kingdom come. Any one of these problems can undermine trust in the process. The sheer volume of problems led us to a point where as of the writing of this article (six days later), the Associated Press still has not declared a winner.
In the case of the Iowa caucuses, the system completely broke down. However, it’s important to note that things don’t actually need to break in order for trust to be broken. As Tom Scott says in the excellent and highly recommended videos below,
“To break an electronic election you don’t actually need to break it. You just have to cast enough doubt on the result.”
Election Security Lessons from Switzerland
In 2022, Andrew Appel from Princeton’s Center for Information Technology Policy published a 5-part series about Switzerland’s e-voting system. The steps required include transcribing a voting key from paper to a browser or app, selecting their candidate(s), and then comparing a return code to their printed sheet. His analysis describes multiple threats, based on a number of hypothetical threats to this protocol.
His warnings went unheeded.
And it gets worse! Recently, Swiss computer scientist Andreas Kuster discovered that the Swiss Post e-voting system had made a basic blunder: the instructions for voting are located on the voting website, which means that if the voter’s computer is compromised by malware, a malicious browser plug-in could alter the behavior of the website.
Appel writes:
Kuster’s fake protocol is not exactly what I imagined; it’s better. He explains it all in his blog post. Basically, in his malware-manipulated website, instead of displaying the verification codes for the voter to compare with what’s on the paper, the website asks the voter to enter the verification codes into a web form. Since the website doesn’t know what’s on the paper, that web-form entry is just for show. Of course, Kuster did not employ a botnet virus to distribute his malware to real voters! He keeps it contained on his own system and demonstrates it in a video.
Kuster immediately notified the Swiss government, who promptly did nothing. Again.
Election Security Lessons from 2020
The lessons are too numerous for a blog post. They deserve a small volume of books from people with more time and expertise than I have. However, the fact that the election results remain so controversial illustrates why electronic voting is such a bad idea. Because it’s invisible and non-auditable, no amount of evidence will ever convince skeptics (there will always be hardcore nonbelievers).
However, when there are paper ballots, even if they’re counted electronically, the system is auditable and unhackable (but not fraud-proof), as demonstrated in the Windham, NH, paper ballot anomaly.
A recent ruling in Georgia by an Obama-appointed judge ruled that cybersecurity flaws violate the rights of voters. Judge Amy Totenberg said that the evidence in the case “does not suggest that the Plaintiffs are conspiracy theorists of any variety.”
“Indeed, some of the nation’s leading cybersecurity experts and computer scientists have provided testimony and affidavits on behalf of Plaintiffs’ case in the long course of this litigation,” she wrote.
She is correct. The mere presence of these flaws is enough to create reasonable doubt of election integrity. Without collective faith in election integrity, there is no democratic process.
OK, Boomer
Former Secretary of State Bill Gardner is regarded by many as a curmudgeonly Luddite. He famously said “You can’t hack a pencil.” And he’s right. I don’t know that he’s received a lot of grief for saying that, but if he has, then he should feel completely vindicated.
I hear a lot of people advocate for Internet voting. In my experience, precisely zero of those people have any experience with cybersecurity. If you know anything about computers, software development, networks, communication protocols, or cybersecurity, you know that these systems have hundreds of attack vectors. The fact of the matter is that hacking a paper ballot system at scale is incredibly difficult to pull off and hide.
Hacking an electronic system is relatively easy and usually undetectable.
Take it from someone with 40 years’ worth of computer, networking, and cybersecurity experience: Anything can be hacked. And the higher the stakes, the more incentive there is and the more likely it becomes.
What About Blockchain?!?
Tom Scott’s video Why Electronic Voting is Still a Bad Idea addresses this. But if you didn’t watch the video, here’s a summary: Blockchain is not magic. It’s a read-only database that doesn’t fundamentally change how the software itself works. It can help assure either trust or anonymity BUT NOT BOTH. And you need both for sound elections.
Here’s another, more humorous way to look at blockchain.
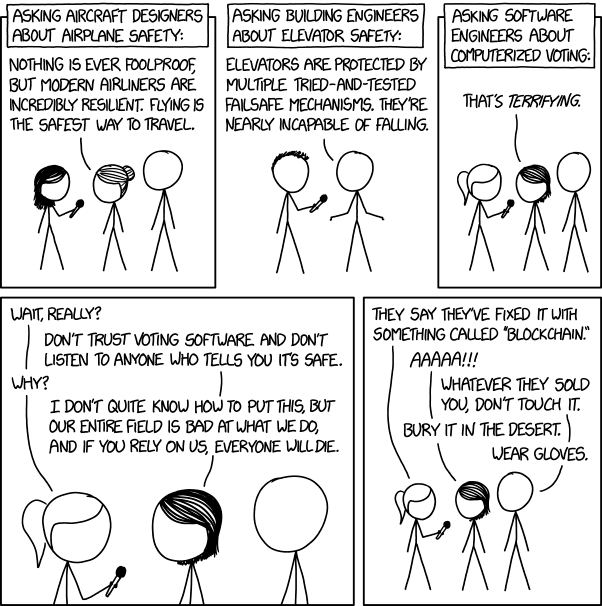
Cybersecurity expert Matt Blaze puts it bluntly here:
Here’s a paper from MIT: Going from Bad to Worse: From Internet Voting to Blockchain Voting
Abstract: Voters are understandably concerned about election security. News reports of possible election interference by foreign powers, of unauthorized voting, of voter disenfranchisement, and of technological failures call into question the integrity of elections worldwide.This article examines the suggestions that “voting over the Internet” or “voting on the blockchain” would increase election security, and finds such claims to be wanting and misleading. While current election systems are far from perfect, Internet- and blockchain-based voting would greatly increase the risk of undetectable, nation-scale election failures.Online voting may seem appealing: voting from a computer or smart phone may seem convenient and accessible. However, studies have been inconclusive, showing that online voting may have little to no effect on turnout in practice, and it may even increase disenfranchisement. More importantly: given the current state of computer security, any turnout increase derived from with Internet- or blockchain-based voting would come at the cost of losing meaningful assurance that votes have been counted as they were cast, and not undetectably altered or discarded. This state of affairs will continue as long as standard tactics such as malware, zero days, and denial-of-service attacks continue to be effective.This article analyzes and systematizes prior research on the security risks of online and electronic voting, and show that not only do these risks persist in blockchain-based voting systems, but blockchains may introduce additional problems for voting systems. Finally, we suggest questions for critically assessing security risks of new voting system proposals.
Conclusion
Electronic voting without paper ballots is a terrible idea. It doesn’t matter how secure the electronic systems are. The mere accusation of a hack is enough to erode confidence. Utilizing paper ballots is the only way to ensure trust, anonymity, and accountability.
Due to multiple and ongoing controversies since 2016, restoring confidence in our elections will require an over-correction in the direction of transparency and accountability. As Scott Adams says,


